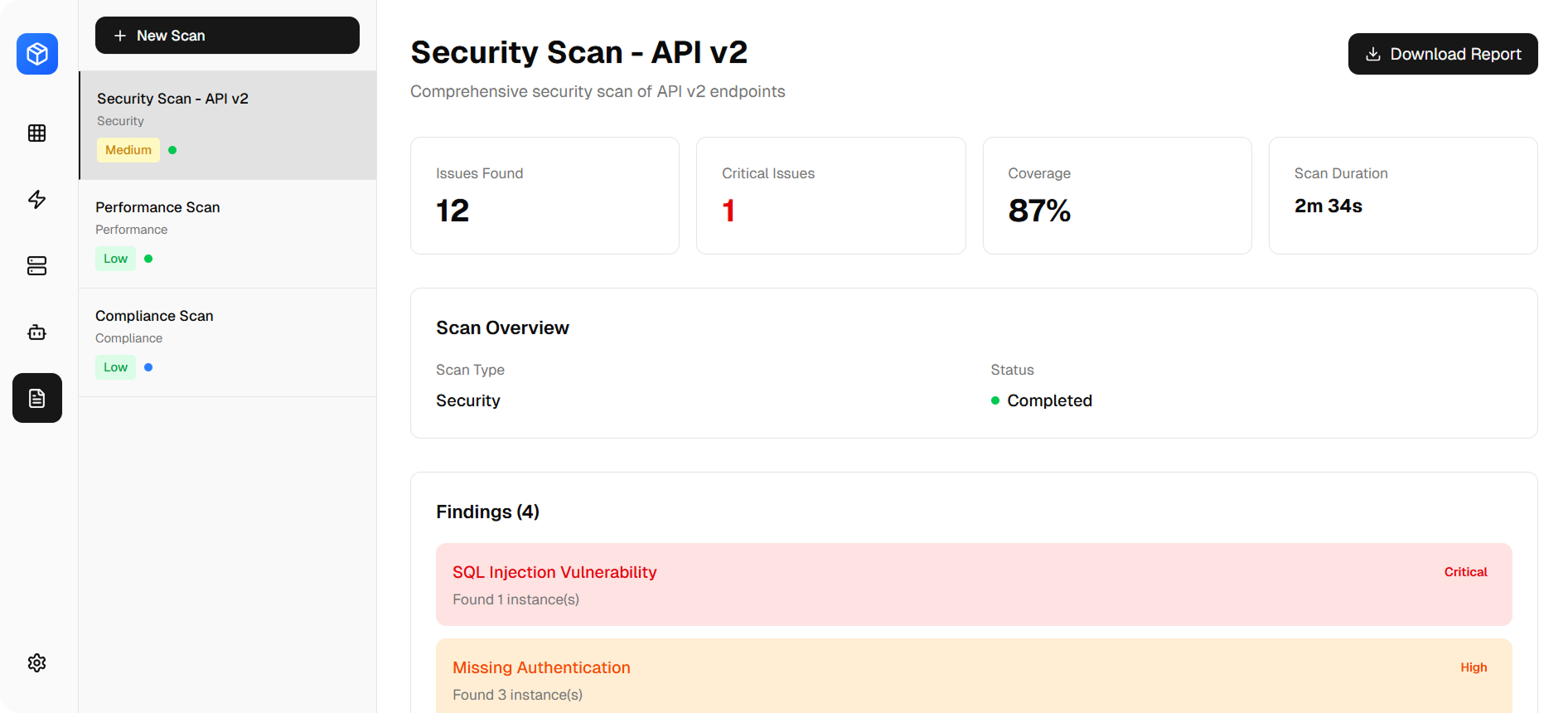
🔍
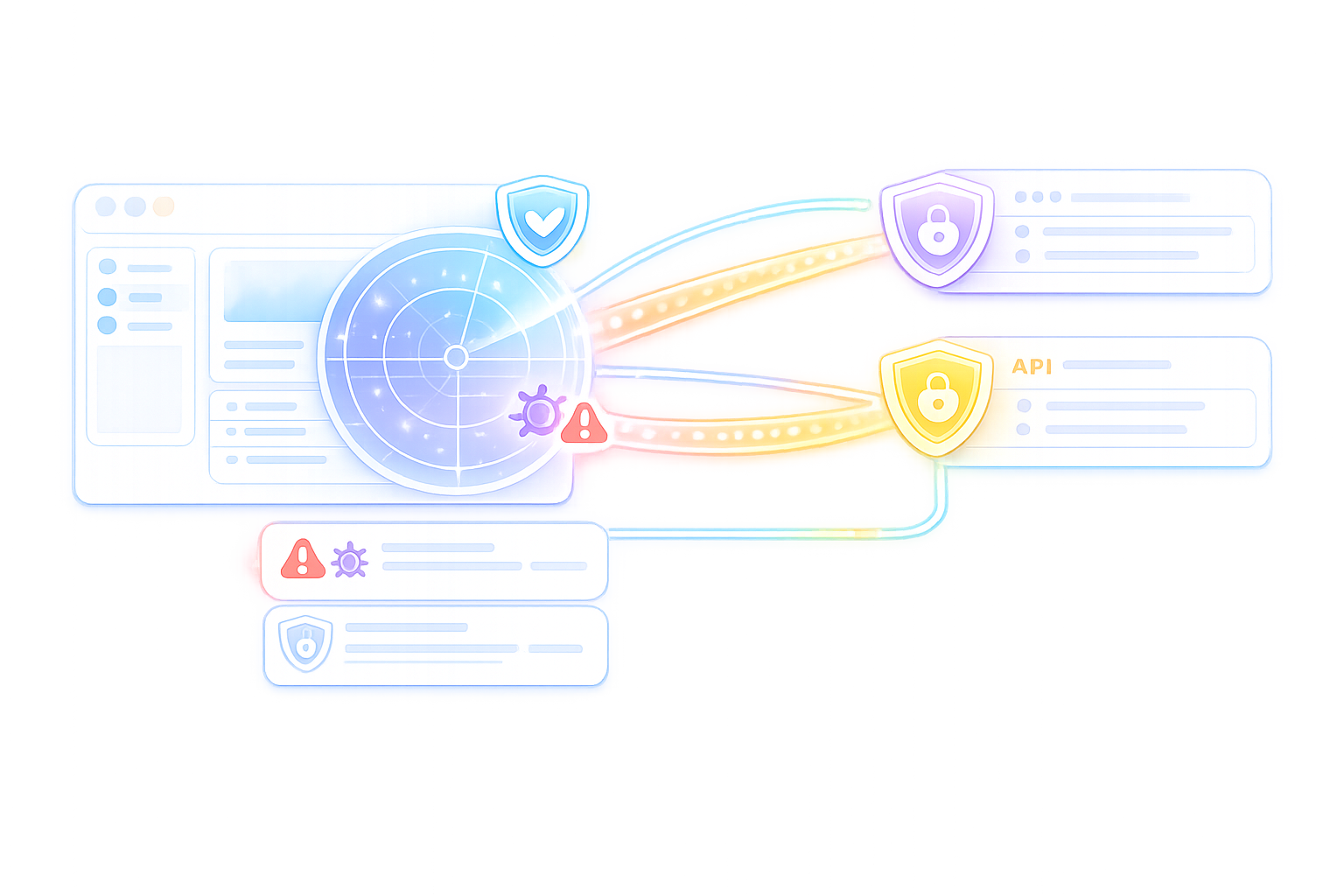
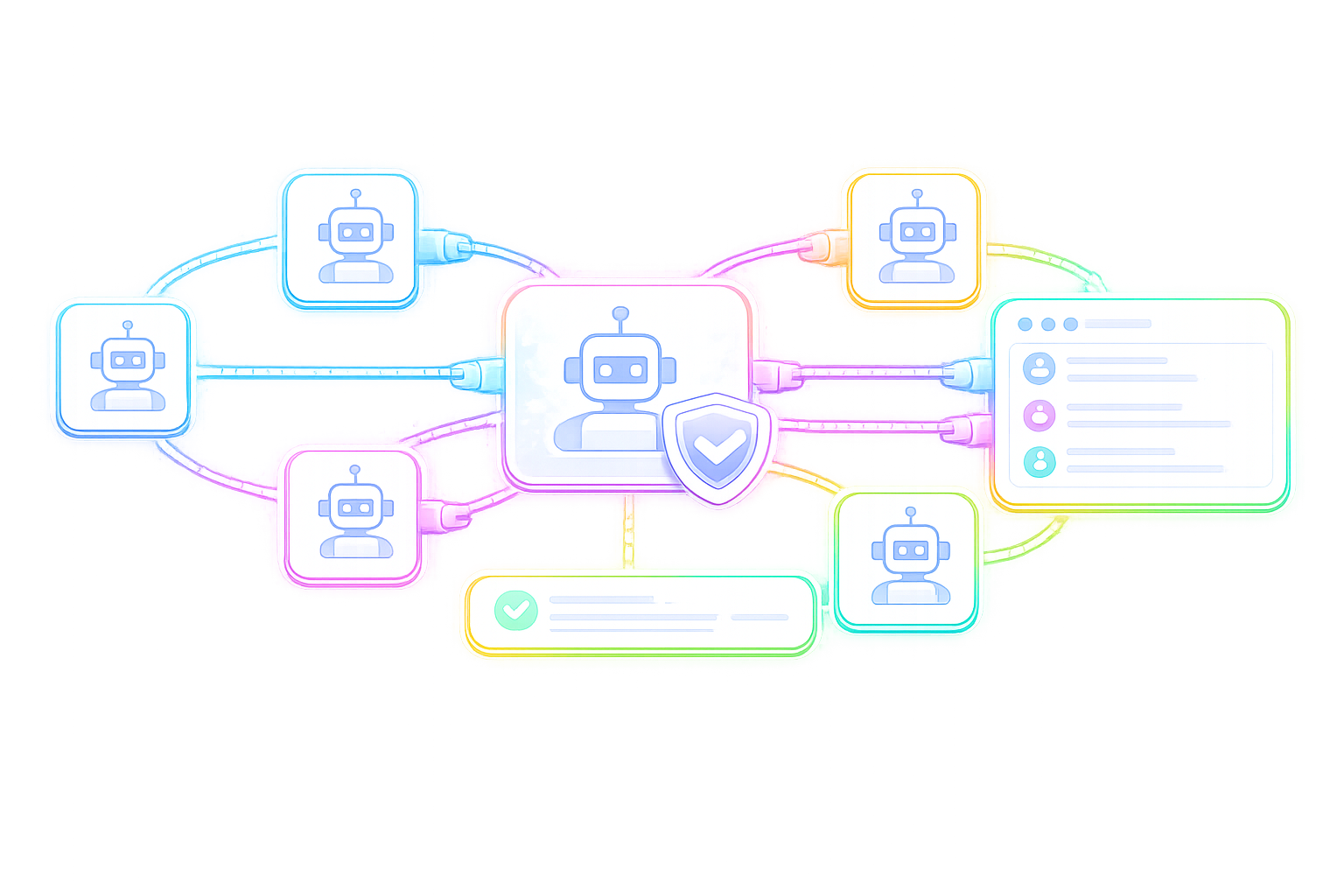
Reconnaissance Agents
Maps attack surface through passive and active discovery. Enumerates subdomains, open ports, service fingerprints, and cloud assets. Builds a comprehensive target graph before any testing begins.
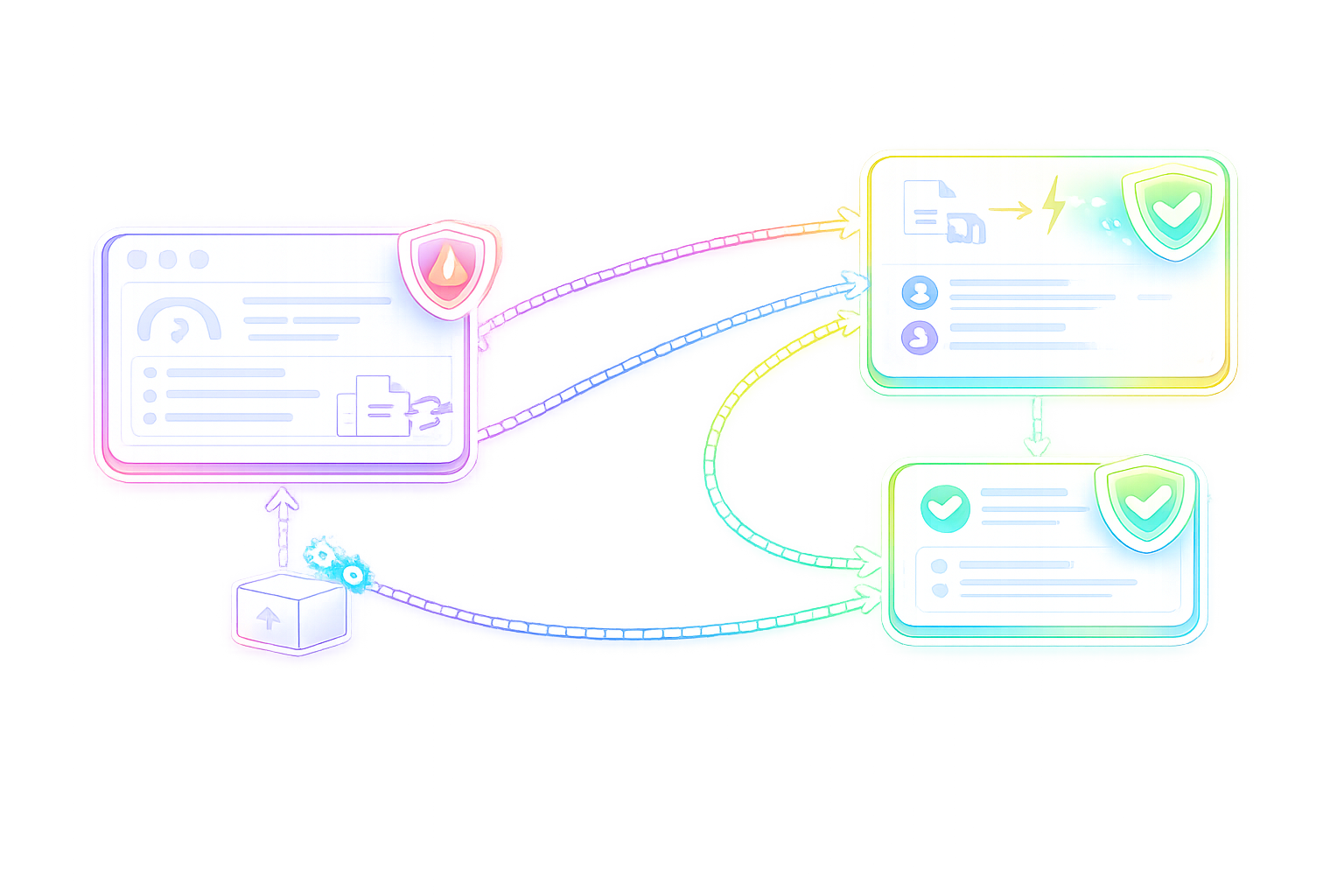
OSINT
DNS Enum
Port Scan
Cloud Discovery